LiteLLM Faces Malicious PyPI Packages in PCP Supply Chain Attack
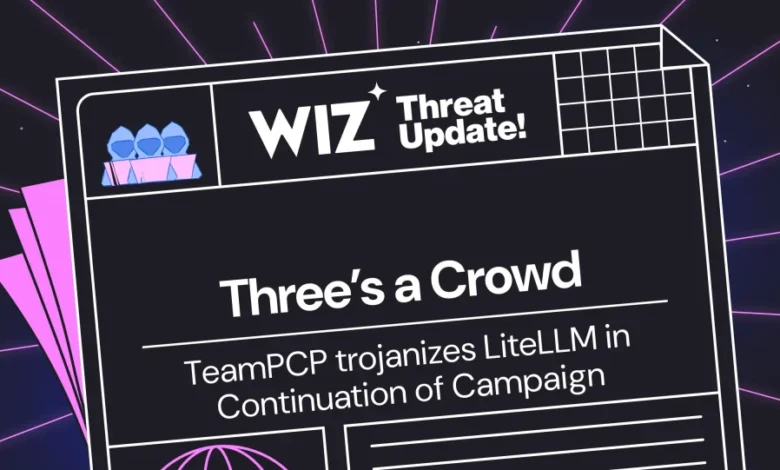
LiteLLM has recently found itself at the center of a malicious attack orchestrated by TeamPCP, posing significant risks to its users. This incident highlights the vulnerabilities within open-source software and the importance of vigilant security practices.
Overview of the Attack on LiteLLM
LiteLLM, a popular open-source Python library, acts as a universal translator for API requests across over 100 large language models, converting them to the standard OpenAI format. It is currently present in 36% of cloud environments, indicating a substantial user base that could be affected by security breaches.
Timeline of Events
- March 24, 2026: Malicious versions of LiteLLM (1.82.7 and 1.82.8) were published.
- 8:30 UTC: The compromised packages became available on PyPI.
- 11:25 UTC: PyPI quarantined the malicious packages.
According to an advisory from PyPI, the breach was traced back to an exposed API token from a prior attack on Aqua Security’s Trivy.
Delivery Methods and Impact
The malicious packages utilized two distinct methods to deliver their payload, targeting various sensitive data on affected hosts. Specifically, they aimed to collect:
- Environment variables, including API keys and tokens
- SSH keys and cloud credentials (AWS, GCP, Azure)
- Kubernetes configurations
- CI/CD secrets
- Docker configurations
- Database credentials
- Cryptocurrency wallets
The data gathered was encrypted using AES-256, with the encryption key further protected by an RSA public key before exfiltration to domains controlled by the attackers.
Security Measures and Recommendations
In response to these incidents, LiteLLM has released a security update to address these vulnerabilities. Users are encouraged to implement the latest updates and review their security measures regularly.
Wiz customers can monitor the ongoing situation through the Wiz Threat Center, where they will find updated guidance, pre-built queries for risk assessment, and resources to secure their environments effectively.
As the open-source community continues to face these challenges, the LiteLLM incident emphasizes the need for robust security practices to safeguard against potential threats.