Quantum Computers Expected to Unveil All Secrets on Day Q
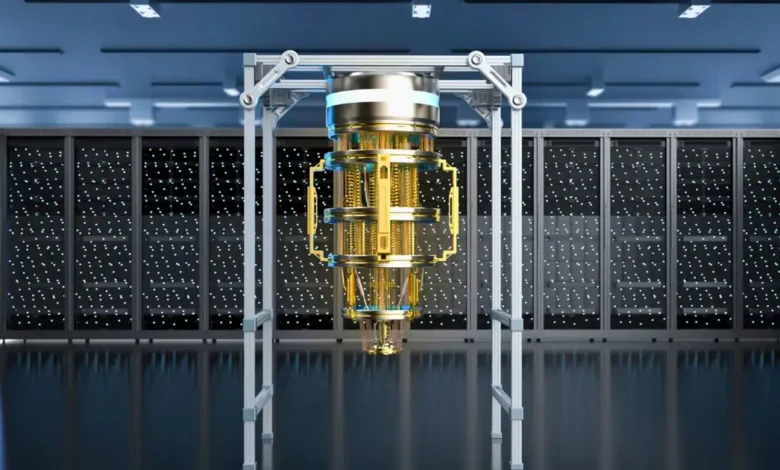
The emergence of quantum computers is set to revolutionize various fields, particularly in data security and cryptography. This technology promises to unveil the secrets behind traditional methods that currently safeguard information.
Quantum Computers and Their Impact on Cryptography
Quantum computers are different from classical computers. They utilize quantum bits, or qubits, which can exist in multiple states at once. This ability allows them to process vast amounts of information simultaneously, making them significantly more powerful.
The RSA Encryption Challenge
Currently, the RSA encryption standard is widely used across the Internet. It employs a public key to encrypt messages and requires a private key for decryption. Conventional computers would take trillions of years to break a 2048-bit RSA key due to their reliance on brute-force methods.
- Time taken by a classical computer to crack RSA-2048: Trillions of years
- Energy consumption: Exceeds global output over extended periods
In contrast, a stable quantum computer utilizing Shor’s algorithm could resolve this encryption in a matter of hours or even seconds. This dramatic improvement highlights the potential vulnerability of existing encryption techniques once quantum computing becomes mainstream.
Shor’s Algorithm: A Game Changer
Developed by mathematician Peter Shor in 1994, Shor’s algorithm facilitates the rapid factorization of large numbers. A quantum computer equipped with just 4,099 stable qubits could break a 2048-bit RSA key in about 10 seconds. This stark contrast raises concerns about the adequacy of current encryption systems in a future dominated by quantum technology.
- Shor’s algorithm speed: 10 seconds for a 2048-bit RSA key with 4,099 qubits
- Classical processing time: 300 trillion years
Current State of Quantum Computing
Despite the significant advancements in quantum computing, the technology is still maturing. The main challenge remains the stability of qubits. Currently, these qubits can lose their quantum state in microseconds, requiring many to be dedicated to error correction.
Experts suggest that millions of physical qubits are needed to achieve the tens of thousands of stable qubits necessary for effective operation of Shor’s algorithm. Estimates on the required number of qubits vary, with some suggesting below one million could be realistic.
According to Michele Mosca, co-founder of the Institute for Quantum Computing at the University of Waterloo, developing fault-tolerant qubits that are resilient against errors and noise is crucial. As various platforms for quantum computers are under development, the timeline to achieve what is known as “Day Q” will heavily depend on which technology proves to be the most scalable and effective.
The Future of Data Security
Although the situation might seem alarming, experts believe there is currently no immediate threat to cryptographic systems. Quantum computers have not yet reached the level of proficiency necessary to compromise existing security measures. However, ongoing research and development in quantum technology signal a need for proactive adaptations in data security protocols.
The quest for encryption methods that can withstand quantum attacks is already underway. As we approach the era of quantum computing, safeguarding our information will require innovative strategies and readiness for the challenges ahead.